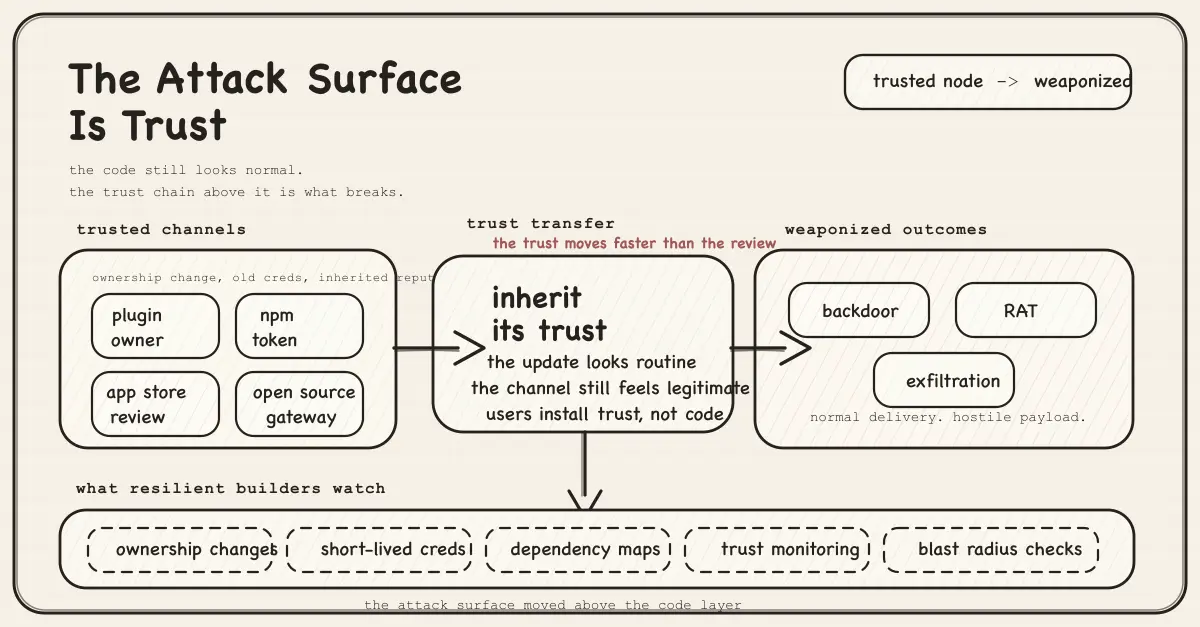
The Attack Surface Is Trust
The most expensive failures are no longer happening in the code itself, but in the trust architecture around it. Supply chains, ownership transfers, and distribution channels are now the real attack surface.
Something shifted in the last ninety days.
Not incrementally. Not in the way security researchers have been warning about for years in conference talks that nobody attends. Shifted in a way that is documented, specific, and already over. The damage done, the infrastructure compromised, the data gone. The pattern is clear enough now that you can name it, and naming it is the first step to building anything that survives what comes next.
The attack surface moved. It is not the code anymore. It is the trust architecture the code sits inside. Who owns the package, who maintains the plugin, which app cleared the review, which library your dependency depends on. That layer is invisible, largely unverified, and almost entirely undefended. And in the last ninety days, every major layer of it got hit simultaneously.
The Playbook
Start with the most surgical example, because it illustrates the pattern with forensic precision.
Someone bought 30 WordPress plugins on Flippa. Legitimate plugins. Real users, real install bases, eight-year-old codebases built by an India-based team called WP Online Support, later rebranded as Essential Plugin. By late 2024, revenue had declined 35-45%. The founder listed the portfolio. A buyer identified only as “Kris” purchased everything for six figures. Flippa published a case study about the sale in July 2025.
The buyer’s very first SVN commit was the backdoor.
Version 2.6.7, released August 8, 2025. The changelog read: “Check compatibility with WordPress version 6.8.2.” What it actually did was add 191 lines of code to a single file: a PHP deserialisation backdoor with an unauthenticated REST API endpoint and an arbitrary function call where the remote server controls the function name, the arguments, everything. It sat dormant for eight months.
On April 6, 2026, between 04:22 and 11:06 UTC, the backdoor activated across every site running any of the 31 affected plugins simultaneously. The malware injected itself into wp-config.php, served SEO spam exclusively to Googlebot (invisible to site owners), and resolved its command-and-control server through an Ethereum smart contract. Traditional domain takedowns are useless against a C2 that lives on a blockchain. The attacker can update the smart contract to point to a new domain at any time. They planned for the remediation too: WordPress.org’s forced patch added return; statements to disable the phone-home mechanism, but it did not touch wp-config.php. The injection kept running on already-compromised sites through a “clean” update.
WordPress.org closed all 31 plugins in a single day. Eight months of dormancy. Six hours and forty-four minutes of active exploitation. Thirty-one plugins gone.
The week before, on March 31, 2026, the Axios npm maintainer account was compromised. The attacker changed the account’s registered email to a ProtonMail address, published two poisoned versions (1.14.1 and 0.30.4), and pre-staged a hidden dependency called plain-crypto-js that dropped a cross-platform RAT across Windows, macOS, and Linux within a 39-minute publish window. Axios has over 100 million weekly downloads. The RAT captured local system data, established persistence, and self-destructed for anti-forensic evasion. Over 10,000 systems were compromised before the packages were pulled.
The same week: TeamPCP poisoned LiteLLM, an open-source AI gateway downloaded 95 million times per month. Mercor, a $10 billion AI recruiting startup that sits inside the data pipelines of OpenAI, Anthropic, and Meta simultaneously, was the primary victim. Roughly 4 terabytes exfiltrated: 939GB of source code, 211GB of user database, 3TB of video interviews, and potentially the proprietary AI training methodologies of multiple frontier labs. Meta paused its Mercor relationship. Anthropic suffered a separate source code leak the same week. One compromised open-source library. Three frontier AI labs. In one afternoon.
Three separate attacks. Different layers, different vectors, different actors. Identical architecture:
Find a trusted node. Inherit its trust. Weaponize it.
The Trust Architecture Nobody Defends
The security apparatus the industry built over the last decade is genuinely good at what it does. Smart contract audits catch reentrancy bugs. Penetration testing finds misconfigured endpoints. Formal verification proves invariants. Bug bounties surface vulnerabilities that internal teams miss. This apparatus was built because the threat was in the code, and it was the right response to the threat that existed in 2015.
The threat moved.
The UK’s AI Security Institute just published its evaluation of Claude Mythos Preview. On expert-level capture-the-flag challenges that no model could complete before April 2025, Mythos succeeds 73% of the time. It became the first model to complete “The Last Ones”, a 32-step corporate network attack simulation spanning initial reconnaissance to full network takeover, estimated to take human professionals 20 hours. It solved it end-to-end in 3 out of 10 attempts. The AISI’s assessment is precise: in environments where attackers can direct a model and provide network access, it can execute multi-stage attacks on vulnerable systems autonomously. Treasury Secretary Bessent and Fed Chair Powell convened the CEOs of Goldman Sachs, Citigroup, Morgan Stanley, Bank of America, and Wells Fargo in person to brief them on these capabilities. Treasury and the Fed do not call emergency bank CEO meetings about software products. They call them about financial stability events. They called one about this.
But here is what the Mythos evaluation actually demonstrates, read alongside the supply chain attacks: the bottleneck for the most dangerous attacks was never computational capability. It was access. The Ethereum C2. The compromised npm account. The Flippa acquisition. The LiteLLM poisoning. None of those required an AI model. They required something simpler and harder to defend against: the patient exploitation of trust relationships that nobody was monitoring.
The Ringmast4r timeline makes this pattern visible at scale. Chinese supercomputer breach: 10 petabytes. Stryker, the surgical robotics company, wiped across 79 countries simultaneously. Lockheed Martin: 375TB claimed. The FBI’s wiretap infrastructure breached, not the inbox, the actual surveillance network used for lawful interception. The FBI Director’s inbox dumped publicly. ShinyHunters, Scattered Spider, and LAPSUS$ formally merged into a single operational alliance called SLH, now operating across 400 organizations. 1.5 billion Salesforce records in one quarter. AI-generated phishing campaigns up 1,265% since 2023.
This is not a list of incidents. It is a documented, coordinated campaign against every layer of digital infrastructure simultaneously: supply chains, financial systems, government networks, AI training pipelines, and the open source stack that holds everything else together.
The Human Layer
The Axios attack and the WordPress acquisition share something the Mythos evaluation does not capture: they did not go through the code. They went through people.
The npm account was not cracked by brute force. It was compromised through a long-lived classic access token, the kind that gets generated once, stored in a config file, forgotten about, and never rotated. The attacker did not need to be clever. They needed patience and a credential that was already exposed.
The Essential Plugin acquisition did not require exploiting a vulnerability. It required six figures, a Flippa account, and the knowledge that WordPress.org has no mechanism to flag or review plugin ownership transfers. No change-of-control notification to users. No additional code review triggered by a new committer. The trust relationship transferred automatically with the asset.
This is the same structural failure as the fake Ledger Live app that sat in Apple’s App Store for six days and drained $9.5 million from 50 victims, three of whom lost seven figures each. A musician named G. Love lost his entire decade of retirement savings in minutes. Not to an exploit. To a text field inside an app that cleared a $3.7 trillion company’s review process. The entire value proposition of a hardware wallet, self-custody and nobody else controls your keys, was undermined by the distribution layer that wrapped it.
Same playbook. Trusted distribution channel. Inherited trust. Weaponized.
Hacken’s Q1 2026 report puts numbers on this pattern: $464.5 million lost across 43 incidents in the first quarter alone. Phishing drove $306 million of that, 81% of the quarterly total. Smart contract exploits: $86 million. Key compromises: $71 million. Resolv had 18 security audits before it was exploited. Venus had 5 audit firms. Combined losses from audited projects: $37.7 million. The CEO’s summary: “the most expensive failures happen outside the code layer entirely.”
The audits are aimed at the wrong layer. The most expensive attacks are happening in the trust architecture the audits never see.
The Pipeline Signal
There is a version of this collapse that is quieter and slower and happening to the developer pipeline itself.
The hackathon circuit, the funnel that was supposed to identify the next generation of serious builders and surface genuine innovation, is being gamed at every layer. Companies use hackathons to farm pivot ideas for free: events with no prizes, stage sermons about changing the world, and mandatory sponsor integrations that consume most of the available build time. Vibe-coders recycle the same project across events week after week, farming wins, accumulating credentials, and landing job offers at companies that then become your coworkers. Tree Hacks found multiple projects with leaked Supabase, OpenAI, and Google API keys committed to public GitHub repos. The commit history that used to flag pre-built projects is now unreadable. Nobody can tell if someone wrote 3,000 lines in an hour through genuine flow or just had Claude do it while they watched.
The trust relationship between “hackathon winner” and “person who can actually build” is broken. Nobody has a mechanism to verify it. And the hiring pipeline downstream is now populated with people whose credentials were earned by gaming a system that stopped having integrity before anyone noticed.
Same failure mode. A trusted signal, plugin provenance, npm package, App Store listing, hackathon credential, gets acquired, inherited, or recycled. The verification mechanism either does not exist or does not catch it in time.
The Ethereum C2 Problem
The most technically significant detail in the WordPress story is the one that received the least attention.
Routing command-and-control through an Ethereum smart contract is not a clever trick. It is a structural escalation. The entire traditional model of incident response, identify the C2 domain, work with registrars and hosting providers to take it down, cut off the attacker’s communication channel, does not work when the C2 lives on a blockchain. You cannot seize a smart contract. You cannot pull a blockchain record. The attacker can update the pointer to a new domain at any time, from anywhere, with no infrastructure to subpoena.
The precedent this sets is significant. If this technique becomes standard, and it will because it works, incident response for supply chain attacks changes permanently. The remediation playbook gets substantially harder. The dormancy window the attacker can maintain gets longer, because there is no C2 domain registration to flag. The blast radius on activation gets larger, because detection and takedown are both slower.
This is an arms race where one side just got a weapon the other side’s existing arsenal cannot neutralize.
What This Means for Builders
None of this is an argument to stop building. The people who understand this layer, who build with the actual risk surface in front of them instead of behind them, are the ones who will build things that hold up.
Concretely, this means treating trust architecture as a first-class engineering problem, not an afterthought.
On dependencies: Every package in your dependency tree has a trust chain behind it. Who maintains it, who has commit access, when they last rotated credentials, whether there has been an ownership change. Most of that chain is invisible by default. Tools like StepSecurity’s Harden-Runner and Socket.dev make it visible. The Axios attack was detected by automated supply-chain monitoring, not by the maintainer, not by npm, but by monitoring infrastructure that was watching for exactly this pattern. If you are not running something equivalent, you are relying on someone else’s monitoring to protect you.
On open source libraries: LiteLLM had 95 million monthly downloads. It was in the dependency tree of a company that trained models for OpenAI, Anthropic, and Meta simultaneously. Nobody at any of those organizations had a complete map of what LiteLLM touched inside their infrastructure until the breach made it visible. Dependency mapping is not optional anymore. It is a precondition for knowing what your blast radius looks like.
On credentials: The Axios attack used a long-lived classic npm access token. Not a zero-day. Not a sophisticated exploit. A token generated once, never rotated, and compromised at some point before the attack. Token rotation, short-lived credentials, hardware-backed authentication: these are solved problems. They just require discipline to maintain. The attacks are not outpacing the defenses here. The defenses are just not being applied consistently.
On acquisition risk: WordPress.org has no mechanism to review plugin ownership transfers. Neither does npm. Neither does the App Store’s review process for apps that clone the branding of legitimate security products. The trust relationship transfers with the asset, automatically, and the users downstream have no way to know it happened. If you are running software whose provenance you have not verified recently, you are trusting a chain you have not checked.
The distributed systems framing that applies to agent pipelines applies here too. Byzantine fault tolerance asks how a network detects and isolates a node that has been compromised and is now sending false information. Most current infrastructure does not have a good answer to that question at the trust layer. The compromised npm package publishes normally. The backdoored plugin updates normally. The fake App Store listing looks legitimate. The failure mode is invisible until it activates.
The builders who treat every external dependency as a potential adversarial node and design accordingly are building something meaningfully more resilient than the ones who do not.
The Actual State of Things
The most consequential hundred days in cyber history are happening while public discourse is mostly elsewhere.
Wiretap infrastructure compromised. Three major criminal groups merged into one operational alliance. A $10 billion AI company that sits inside three frontier labs’ training pipelines breached through a single open-source library. An AI model that can autonomously execute multi-stage corporate network attacks, good enough that the Treasury Secretary and the Fed Chair called emergency meetings with bank CEOs about it.
And underneath all of it: a systematic, patient, coordinated exploitation of the trust relationships that every piece of digital infrastructure depends on. Plugin marketplaces, package registries, app stores, maintainer credentials, acquisition channels, hiring pipelines.
The attack surface is not the code. It never really was the only surface. It was just the most visible one, and the industry built its defenses there because that is where the light was.
The trust architecture is the real surface. It is largely unmapped, largely undefended, and actively being exploited right now at every layer simultaneously.
That is not the alarming version of events. That is the accurate one.
The agents are shipped. The code is audited. The foundations, the trust layer that holds everything else together, still need to be built.
Written by Nirav Joshi · Fullstack and Blockchain Developer
Newsletter
Want the next post like this?
Subscribe for occasional emails when I publish something worth your time.